Unlocking EBS Encryption: Your Deep Dive Into AWS Data-at-Rest Security
How AWS uses a "key-to-encrypt-a-key" strategy to keep your block storage iron-clad.
In modern cloud architecture, security is a multi-layered discipline. While network-level controls like VPCs and Security Groups secure the perimeter, and IAM policies manage access, the integrity of data at rest remains a fundamental pillar of a robust security posture. For services relying on Amazon’s Elastic Compute Cloud (EC2), this concern is directly addressed by Elastic Block Store (EBS) Encryption.
Many users enable this feature—often by simply checking a box—without fully comprehending the sophisticated and seamless cryptographic process operating beneath the surface. This article provides a comprehensive, architectural breakdown of EBS encryption, demystifying its “envelope encryption” model, the detailed read/write lifecycle, and the critical role of the AWS Key Management Service (KMS).
What is EBS Encryption? A Formal Definition
Amazon EBS provides persistent block-level storage volumes for use with EC2 instances. By default, data on a newly created EBS volume is unencrypted. EBS encryption is a feature that enables transparent, hardware-accelerated encryption of this data.
When enabled, EBS encryption provides a comprehensive solution that covers:
Data at Rest: All data stored on the EBS volume is encrypted using the industry-standard AES-256-XTS algorithm.
Data in Transit: All data moving between the EC2 instance and its attached EBS volume is automatically encrypted while in transit within the AWS private network.
Snapshots: All snapshots created from an encrypted volume are inherently encrypted.
Child Volumes: All volumes created from an encrypted snapshot are, by default, also encrypted.
Critically, on all modern EC2 instance types, the encryption and decryption processes are offloaded to dedicated hardware (leveraging CPU extensions like Intel AES-NI). This minimizes the performance overhead, making the security benefit virtually “free” in terms of computational impact.
The Core Architectural Pattern: Envelope Encryption
To understand EBS encryption, one must first understand its underlying cryptographic strategy: Envelope Encryption.
This is a key management practice that avoids the high risk and overhead of encrypting petabytes of data with a single master key. Instead, it uses a two-tiered system:
Data Encryption Key (DEK): This is a unique, symmetric AES-256 key generated by AWS for each individual EBS volume. This “workhorse” key is responsible for the actual encryption and decryption of the data blocks on that specific volume.
Key Encryption Key (KEK): This is the “master key” (referred to in AWS as a KMS Key) stored and managed within the AWS Key Management Service (KMS). Its sole purpose is to encrypt and decrypt the Data Encryption Keys (DEKs).
The process, at a high level, is as follows:
Your data is encrypted by the DEK.
The DEK is encrypted by the KMS Key.
This encrypted DEK (known as a
CiphertextBlob) is then stored as metadata alongside the encrypted volume.
This “envelope” strategy provides immense security and operational benefits:
Minimized Key Exposure: The powerful KMS Key never leaves the confines of the FIPS 140-2 validated hardware security modules (HSMs) within KMS. It is only used to encrypt/decrypt the much smaller DEKs.
Granular Access Control: Access to data is now governed by access to the KMS Key. By controlling who can use the KMS Key (via IAM and Key Policies), you control who can decrypt the DEK and therefore read the volume.
Simplified Key Rotation: To “rotate” the key for a volume, you only need to re-encrypt the DEK with a new KMS Key, not re-encrypt the entire multi-terabyte volume.
The Detailed Cryptographic Workflow (Read/Write Lifecycle)
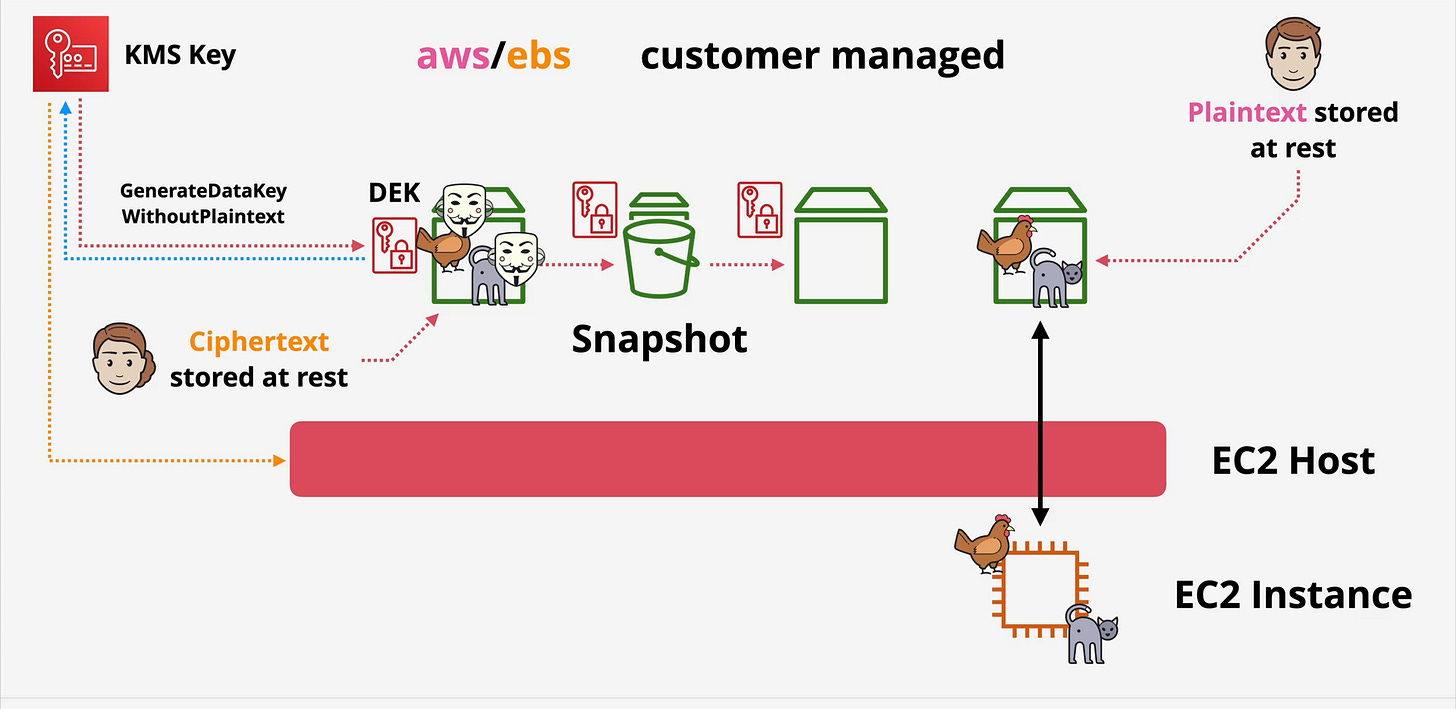
The true mechanics of EBS encryption are orchestrated by the physical EC2 Host—the underlying hypervisor—on which your EC2 instance runs. Your instance’s operating system is completely abstracted from this process.
Let’s analyze the complete lifecycle.
Part 1: Volume Creation and Attachment
Request: A user requests a new encrypted EBS volume, specifying a KMS Key (either the AWS-managed default or a Customer Managed Key).
Key Generation: The EC2 Host, acting on your behalf, makes a
GenerateDataKeyAPI call to KMS against your specified KMS Key.KMS Response: KMS returns two distinct objects to the EC2 Host:
Plaintext: A new, unique plaintext Data Encryption Key (DEK).CiphertextBlob: The same DEK, but encrypted by the specified KMS Key.
Storage and Caching:
The EC2 Host stores the
CiphertextBlob(the encrypted DEK) as metadata with the EBS volume.The EC2 Host caches the
PlaintextDEK securely in its own temporary memory.
Part 2: Runtime Write Operation
Application Write: Your application (e.g., a database) running on the EC2 instance writes data.
Transparent Encryption: This data is passed from the EC2 instance to the underlying EC2 Host. The Host’s hypervisor intercepts this I/O operation.
DEK Usage: The Host uses the
PlaintextDEK (cached in its memory) to encrypt the data block.Commit to Storage: This newly encrypted data block is written to the physical EBS storage medium.
At no point does the Plaintext DEK or the unencrypted application data ever touch the disk.
Part 3: Runtime Read Operation
Application Read: Your application requests a block of data.
Fetch Encrypted Data: The EC2 Host reads the encrypted data block from the EBS volume.
Transparent Decryption: The Host uses the same
PlaintextDEK from its memory cache to decrypt the data block.Data Return: The Host returns the resulting plaintext data to your EC2 instance.
Part 4: Volume Detach/Re-Attach (The “Decrypt” Operation)
This is the most critical part of the security model.
Key Flush: When the EC2 instance is stopped or the volume is detached, the
PlaintextDEK is purged from the EC2 Host’s memory. All that remains is theCiphertextBlob(encrypted DEK) stored with the volume.Volume Re-Attach: When you start the instance or re-attach the volume (potentially to a completely different EC2 Host), the new Host must gain access to the
PlaintextDEK.KMS Decrypt Call: The new Host reads the
CiphertextBlobfrom the volume’s metadata. It then makes aDecryptAPI call to KMS, presenting thisCiphertextBloband its own IAM credentials.Authorization Check: KMS performs a rigorous authorization check:
Does the IAM Role of this EC2 Host have permission to perform the
kms:Decryptaction?Does the Key Policy on the KMS Key also allow this role to use the key for decryption?
Key Return: If and only if both checks pass, KMS uses the master key to decrypt the
CiphertextBloband returns thePlaintextDEK to the EC2 Host.Caching: The Host caches this
PlaintextDEK in memory, and normal read/write operations (Parts 2 & 3) can now resume.
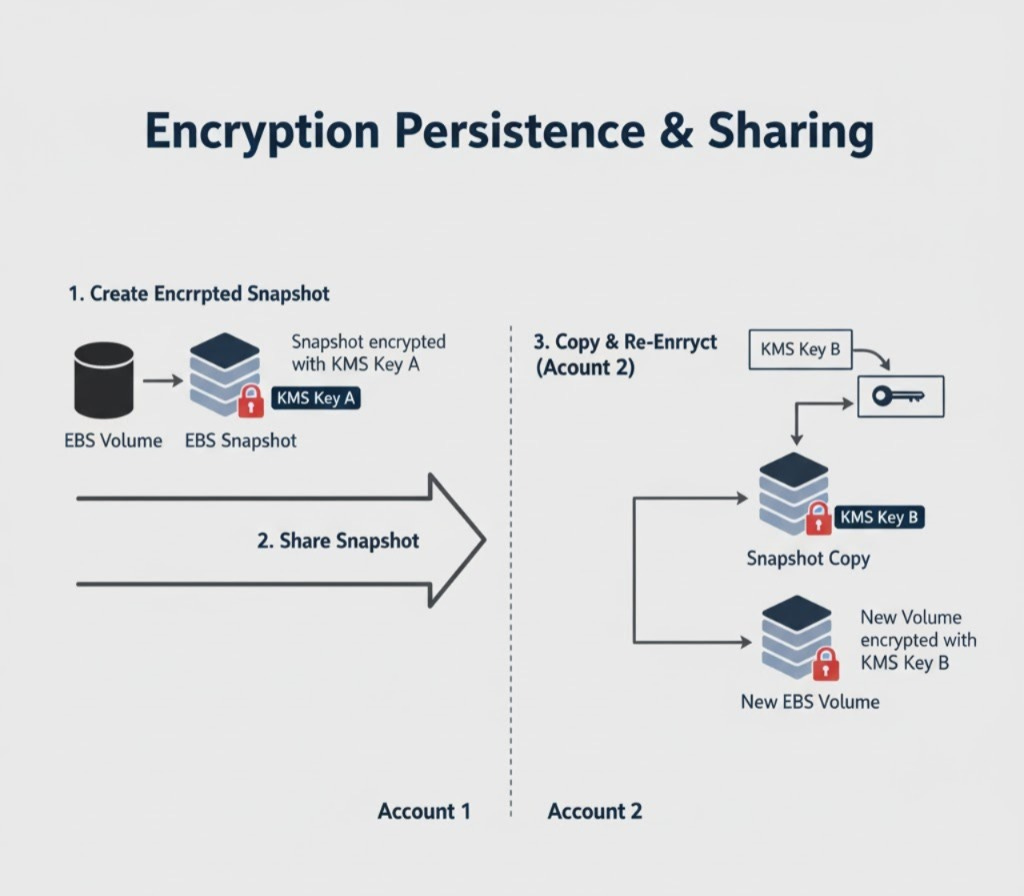
Encryption Persistence (Snapshots and Cross-Account Sharing)
The EBS encryption model extends seamlessly to snapshots, which is fundamental for backups and disaster recovery.
When you snapshot an encrypted volume, the snapshot is encrypted by default. It stores not only the encrypted data blocks but also a copy of the volume’s
CiphertextBlob(the encrypted DEK).When you restore a snapshot to a new volume, a new
GenerateDataKeycall is made. This creates a brand new, unique DEK for the new volume.AWS then performs an internal, server-side re-encryption:
Calls
Decrypton the snapshot’s DEK (using the original KMS Key).Uses this key to decrypt the snapshot data.
Uses the new volume’s DEK to re-encrypt the data as it’s written to the new volume.
This re-encryption mechanism is the foundation for securely sharing encrypted snapshots. You cannot simply share an encrypted snapshot; you must:
Share the snapshot, and grant the target account
kms:Decryptpermissions on the original KMS Key.The target account must then copy the snapshot, specifying their own KMS Key during the copy.
AWS will perform the re-encryption flow, creating a new snapshot in the target account encrypted with their key. At this point, permissions on the original key can be revoked.
Key Management: AWS Managed vs. Customer Managed Keys
The final component of this architecture is your choice of KMS Key, which dictates your level of control, auditing capability, and cost. The first option is the AWS Managed Key (specifically aws/ebs), which is free, created, and entirely managed by AWS. While this provides a simple, “set-it-and-forget” solution with automatic key rotation, it comes with significant limitations: you cannot modify its access policy, and most importantly, its usage (such as Decrypt or GenerateDataKey calls) is not logged in your account’s CloudTrail. This makes it suitable for basic, non-sensitive workloads but insufficient for compliance. The second and more robust option is the Customer Managed Key (CMK). With a CMK, you create, own, and fully manage the key, incurring standard KMS fees for storage and API usage. This provides complete, granular control over access through both IAM and Key Policies. The critical differentiator is that all API calls using your CMK are fully auditable in AWS CloudTrail, providing a detailed log of who used what key and when. This auditability, combined with manageable rotation schedules, makes CMKs the essential choice for regulated workloads (e.g., PCI, HIPAA), multi-account sharing strategies, and any environment demanding a provable, high-security posture.
Conclusion: A Foundational Pillar of Defense-in-Depth
EBS encryption is a powerful, high-performance security feature that provides robust protection for data at rest. Its envelope encryption architecture elegantly separates the high-stakes management of master keys (in KMS) from the high-throughput cryptographic operations (on the EC2 Host).
By understanding this workflow, a “simple” checkbox evolves into a clear component of your security strategy. You can now make informed decisions about key management (AWS vs. Customer Managed) and confidently design secure, auditable, and compliant data architectures on AWS.
For all AWS users, the immediate, actionable recommendation is to enable “Encrypt by Default” in your account’s EC2 settings for all regions. This ensures all new volumes are encrypted, providing a foundational security uplift with no performance cost.